Много опции с един доверен ИТ партньор – LIREX!
Клиентите ни получават 360-градусов спектър от ИТ решения и услуги. Използвайки правилните технологии, подходи и богатото си портфолио, ние успяваме да отговорим на потребностите на клиентите си през различните етапи на всеки проект.
Иновативното мислене e в нашето ДНК. Ние изграждаме решения, в които вярваме – нашата страст за иновация движи както нашият прогрес и развитие, така и тези на нашите клиенти. Вярваме в опростеното, а не в сложното. Действаме предприемчиво и въвеждаме смели ИТ решения.
LIREX предлага технологии на топ производители, персонализирани решения и услуги, ИТ експертиза в съчетание с високо ниво на обслужване. Нашият гъвкав подход за интеграция позволява на клиентите ни да имат нарастващ избор и комплексни, персонализирани решения, максимално точно отговарящи на потребностите им. Ние никога не спираме да работим с и за вас.
Комбинация от ИТ предложения, които покриват голям спектър от вашите бизнес потребности
LIREX е една от малкото компании, която предлага портфолио от ИТ решения и услуги, покриващо 3 ключови потребности.
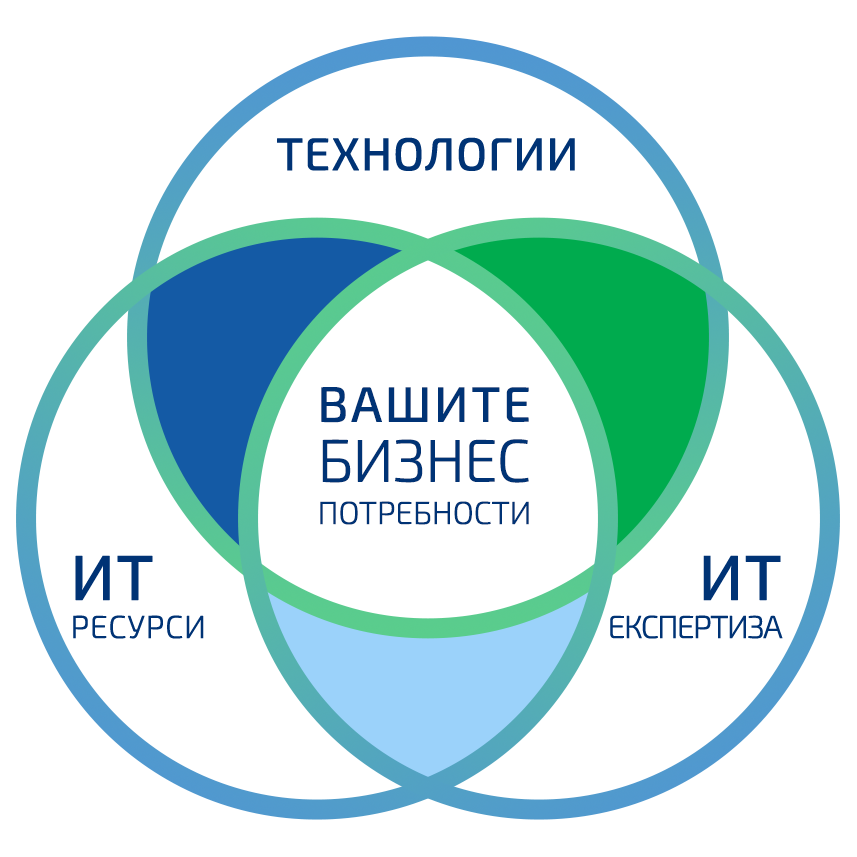
Иновативни технологии, грижливо подбрани в пълна палитра от топ технологични партньори, осигурявайки ви достъп до решения с най-високото качество.
Партнираме си с топ производители, грижливо подбирайки подходящия микс от технологии, така че да отговорим на изискванията на нашите клиенти.
Инвестицията на LIREX да изгради динамична екосистема от доверени партньори ни позволява изцяло да гарантираме наличие и овладяване на най-новите технологии и съвременни ИТ решения.
ИТ експерти до най-високо ниво в разнообразни области, работещи в сътрудничество с вас за предоставяне на необходимите експертни познания и консултации.
С LIREX получавате пълен набор от услуги, свързани с въвеждането на нови решения: дизайн, архитектура, избор на решение, спецификация, пускане в експлоатация, конфигуриране и поддръжка.
А също и експертиза, свързана със сигурността като ИТ одити, пен тестове, правила, политики и процедури
Технически компетенции за качествена и прецизна реализация на всеки проект и локация, включително и вашите надеждни „ръце на място“, които ви дават гъвкавост и спокойствие.
При неравномерни или пикови натоварвания в обема работа на ИТ отдела или необходимост от техници и инженери във всеки ваш обект можете да разчитате на нас. Специалистите на LIREX ви помагат с проекти за планово обновяване на хардуер, пускане в експлоатация на ново решение или осигуряване на поддръжка на текущото в цялата страна.
Новости и тенденции в ИТ
Технологичният свят е особено динамичен, иновациите са случват по-бързо от всякога, а с това и възможностите, които предлагат се увеличават. Технологиите вече са далеч повече от инструмент, който подпомага дейността.
Те са често ключова част от реализацията на различни стратегически инициативи, и оптимизацията на вътрешни и административни процеси.

 English
English